The notorious cryptojacking group tracked as 8220 Gang has been spotted weaponizing a six-year-old security flaw in Oracle WebLogic servers to ensnare vulnerable instances into a botnet and distribute cryptocurrency mining malware.
The flaw in question is CVE-2017-3506 (CVSS score: 7.4), which, when successfully exploited, could allow an unauthenticated attacker to execute arbitrary commands remotely.
8220 Gang, first documented by Cisco Talos in late 2018, is so named for its original use of port 8220 for command-and-control (C2) network communications.
Earlier this year, Sydig detailed attacks mounted by the “low-skill” crimeware group between November 2022 and January 2023 that aim to breach vulnerable Oracle WebLogic and Apache web servers and deploy a cryptocurrency miner.

It has also been observed making use of an off-the-shelf malware downloader known as PureCrypter as well as a crypter codenamed ScrubCrypt to conceal the miner payload and evade detection by security software.
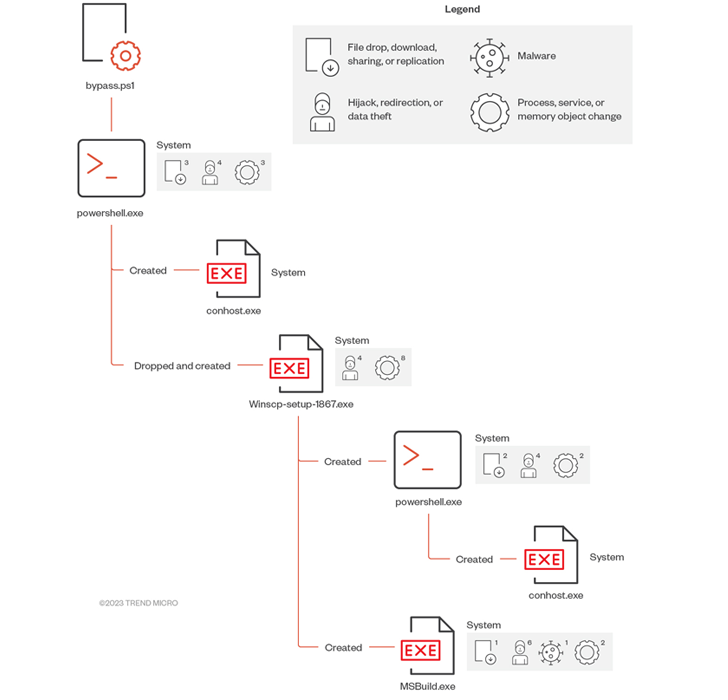
In the latest attack chain documented by Trend Micro, the Oracle WebLogic Server vulnerability is leveraged to deliver a PowerShell payload, which is then used to create another obfuscated PowerShell script in memory.
The intermediate DLL file, for its part, is configured to download a cryptocurrency miner from one of the three C2 servers – 179.43.155[.]202, work.letmaker[.]top, and su-94.letmaker[.]top – using TCP ports 9090, 9091, or 9092.
Trend Micro said recent attacks have also entailed the misuse of a legitimate Linux tool called lwp-download to save arbitrary files on the compromised host.
Source: https://thehackernews.com/