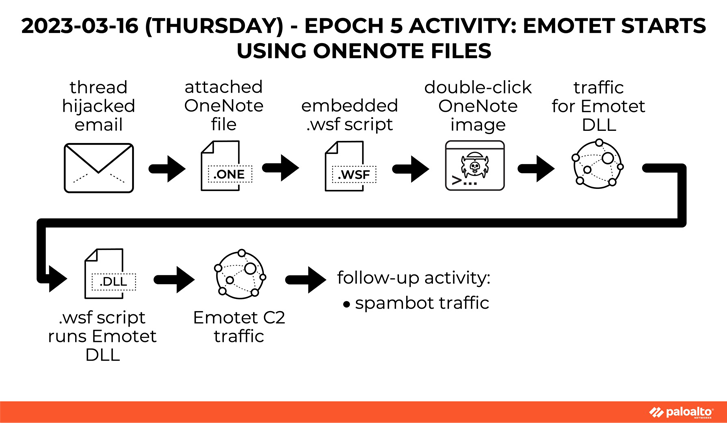
The notorious Emotet malware, in its return after a short hiatus, is now being distributed via Microsoft OneNote email attachments in an attempt to bypass macro-based security restrictions and compromise systems.
Emotet, linked to a threat actor tracked as Gold Crestwood, Mummy Spider, or TA542, continues to be a potent and resilient threat despite attempts by law enforcement to take it down.
While Emotet infections have acted as a conduit to deliver Cobalt Strike, IcedID, Qakbot, Quantum ransomware, and TrickBot, its return in late 2021 was facilitated by means of TrickBot.
“Emotet is known for extended periods of inactivity, often occurring multiple times per year, where the botnet maintains a steady-state but does not deliver spam or malware,” Secureworks notes in its profile of the actor.

The Windows Script File (WSF) is engineered to retrieve and execute the Emotet binary payload from a remote server. Similar findings have been echoed by Cyble, IBM X-Force, and Palo Alto Networks Unit 42.
Such documents have been observed to leverage a technique called decompression bomb to conceal a very large file (over 550 MB) within ZIP archive attachments to fly under the radar, according to multiple reports from Cyble, Deep Instinct, Hornetsecurity, and Trend Micro.
The latest development is a sign of the operators’ flexibility and agility in switching attachment types for initial delivery to evade detection signatures. It also comes amid a spike in threat actors using OneNote documents to distribute a wide range of malware such as AsyncRAT, Icedid, RedLine Stealer, Qakbot, and XWorm.
Source: https://blog.bughunters.am/