An Android voice phishing (aka vishing) malware campaign known as FakeCalls has reared its head once again to target South Korean users under the guise of over 20 popular financial apps.
“FakeCalls malware possesses the functionality of a Swiss army knife, able not only to conduct its primary aim but also to extract private data from the victim’s device,” cybersecurity firm Check Point said.
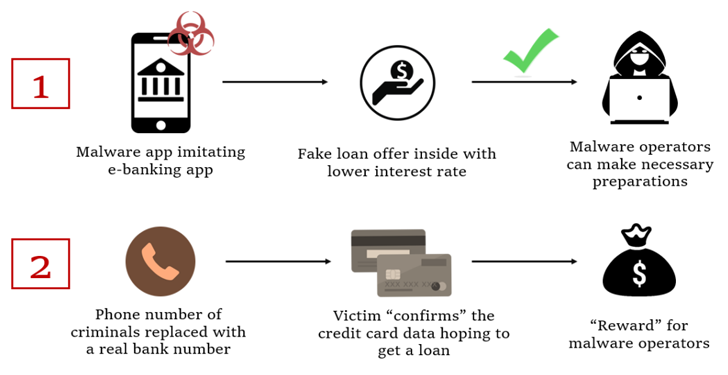
At the point where the phone call actually happens, a pre-recorded audio with instructions from the real bank is played. Simultaneously, the malware conceals the phone number with the bank’s legitimate number to give the impression that a conversation is happening with an actual bank employee on the other end.
The ultimate goal of the campaign to get the victim’s credit card information, which the threat actors claim is required to qualify for the non-existent loan.
The latest FakeCalls samples further implement various techniques to stay under the radar. One of the methods involves adding a large number of files inside nested directories to the APK’s asset folder, causing the length of the file name and path to breach the 300-character limit.

The development is part of a growing trend where threat actors have unleashed increasingly sophisticated banking malware to automate the whole process of unauthorized money transfers on infected devices.
“Despite the decline in overall malware installers, the continued growth of mobile banking Trojans is a clear indication that cybercriminals are focusing on financial gain,” Kaspersky researcher Tatyana Shishkova said.
Source: https://thehackernews.com/