A North Korean government-backed threat actor has been linked to attacks targeting government and military personnel, think tanks, policy makers, academics, and researchers in South Korea and the U.S.
Google’s Threat Analysis Group (TAG) is tracking the cluster under the name ARCHIPELAGO, which it said is a subset of another threat group tracked by Mandiant under the name APT43.
The tech giant said it began monitoring the group in 2012, adding it has “observed the group target individuals with expertise in North Korea policy issues such as sanctions, human rights, and non-proliferation issues.”
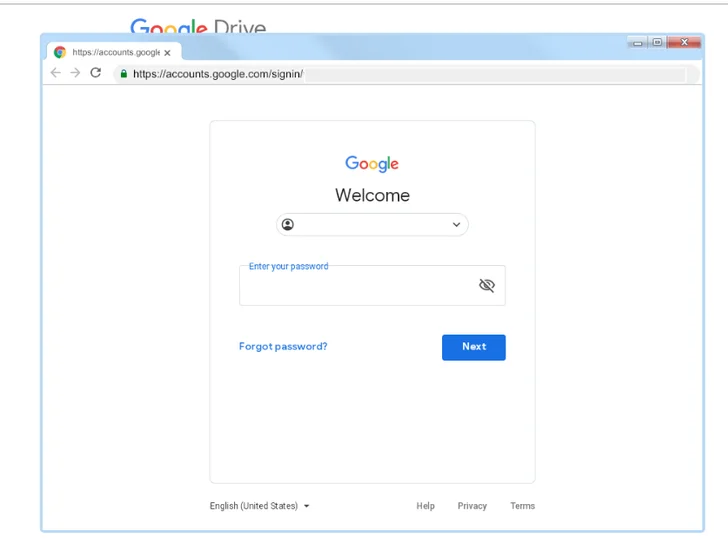
Attack chains mounted by ARCHIPELAGO involve the use of phishing emails containing malicious links that, when clicked by the recipients, redirect to fake login pages that are designed to harvest credentials.

What’s more, the phishing messages have posed as Google account security alerts to activate the infection, with the adversarial collective hosting malware payloads like BabyShark on Google Drive in the form of blank files or ISO optical disc images.
Another notable technique adopted by ARCHIPELAGO is the use of fraudulent Google Chrome extensions to harvest sensitive data, as evidenced in prior campaigns dubbed Stolen Pencil and SharpTongue.
The development comes as AhnLab Security Emergency Response Center (ASEC) detailed Kimsuky’s use of Alternate Data Stream (ADS) and weaponized Microsoft Word files to deliver info-stealer malware.
Source: https://thehackernews.com/