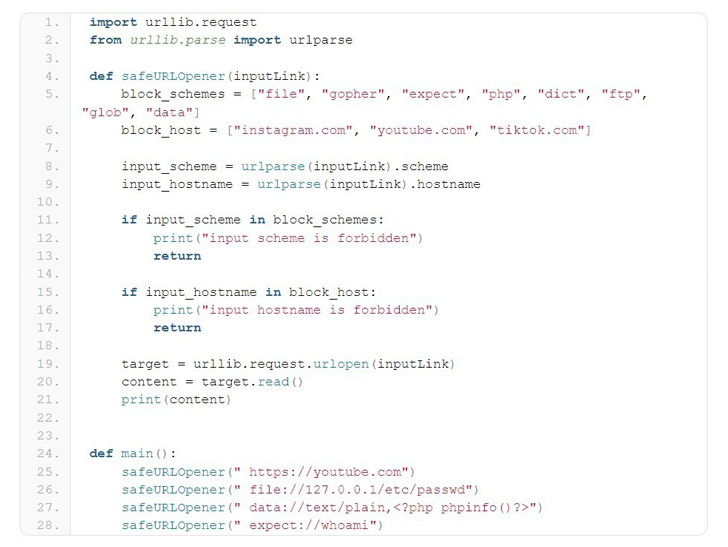
A high-severity security flaw has been disclosed in the Python URL parsing function that could be exploited to bypass domain or protocol filtering methods implemented with a blocklist, ultimately resulting in arbitrary file reads and command execution.
“urlparse has a parsing problem when the entire URL starts with blank characters,” the CERT Coordination Center (CERT/CC) said in a Friday advisory. “This problem affects both the parsing of hostname and scheme, and eventually causes any blocklisting methods to fail.”

The flaw has been assigned the identifier CVE-2023-24329 and carries a CVSS score of 7.5. Security researcher Yebo Cao has been credited with discovering and reporting the issue in August 2022. It has been addressed in the following versions –
- >= 3.12
- 3.11.x >= 3.11.4
- 3.10.x >= 3.10.12
- 3.9.x >= 3.9.17
- 3.8.x >= 3.8.17, and
- 3.7.x >= 3.7.17
urllib.parse is a widely used parsing function that makes it possible to break down URLs to its constituents, or alternatively, combine the components to a URL string.
The disclosure comes as new research found that security fixes in Python often occur through “silent” code commits, without an associated Common Vulnerabilities and Exposures (CVE) identifier, thereby providing malicious actors an opportunity to potentially exploit undisclosed vulnerabilities in unpatched systems.
Source: https://thehackernews.com/