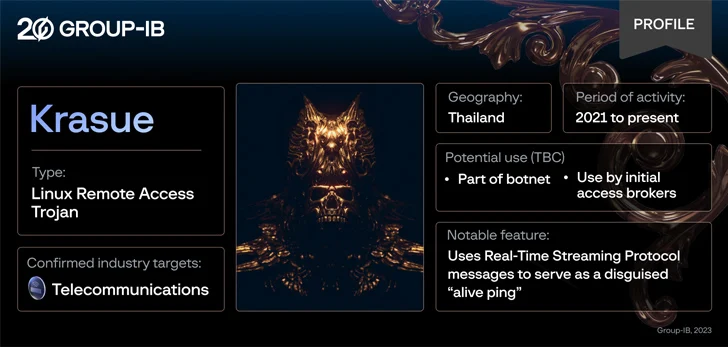
A previously unknown Linux remote access trojan called Krasue has been observed targeting telecom companies in Thailand by threat actors to main covert access to victim networks at lease since 2021.
Named after a nocturnal female spirit of Southeast Asian folklore, the malware is “able to conceal its own presence during the initialization phase,” Group-IB said in a report shared with The Hacker News.
The exact initial access vector used to deploy Krasue is currently not known, although it’s suspected that it could be via vulnerability exploitation, credential brute-force attacks, or downloaded as part of a bogus software package or binary.
“The rootkit can hook the `kill()` syscall, network-related functions, and file listing operations in order to hide its activities and evade detection,” Group-IB malware analyst Sharmine Low said.

“Notably, Krasue uses RTSP (Real Time Streaming Protocol) messages to serve as a disguised ‘alive ping,’ a tactic rarely seen in the wild.”
The trojan’s command-and-control (C2) communications further allow it to designate a communicating IP as its master upstream C2 server, get information about the malware, and even terminate itself.
Krasue also shares several source code similarities with another Linux malware named XorDdos, indicating that it has been developed by the same author as the latter, or by actors who had access to its source code.
Group-IB told The Hacker News that it has so far identified one confirmed case, and that it’s investigating three other potential incidents in which the malware has been used. But it’s suspected that the number of companies targeted could be higher.
Source: https://thehackernews.com/