More than a dozen malicious packages have been discovered on the npm package repository since the start of August 2023 with capabilities to deploy an open-source information stealer called Luna Token Grabber on systems belonging to Roblox developers.
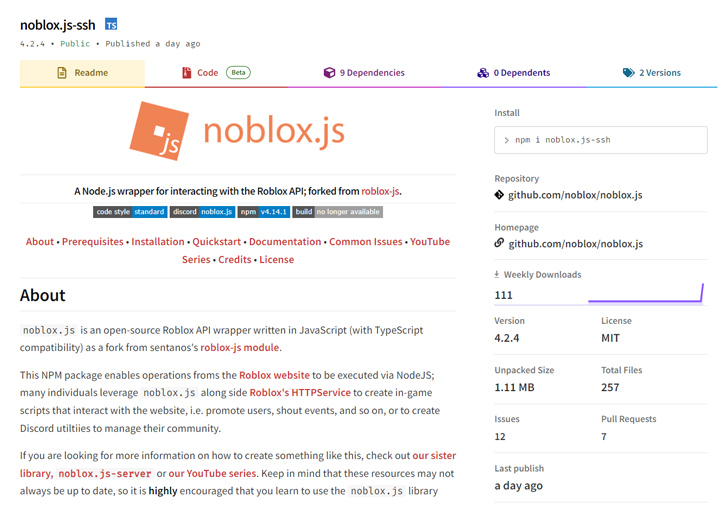
The ongoing campaign, first detected on August 1 by ReversingLabs, employs modules that masquerade as the legitimate package noblox.js, an API wrapper that’s used to create scripts that interact with the Roblox gaming platform.
The software supply chain security company described the activity as a “replay of an attack uncovered two years ago” in October 2021.
The packages were cumulatively downloaded 963 times before they were taken down. The names of the rogue packages are as follows –
- noblox.js-vps (versions 4.14.0 to 4.23.0)
- noblox.js-ssh (versions 4.2.3 to 4.2.5)
- noblox.js-secure (versions 4.1.0, 4.2.0 to 4.2.3)

The modules, in particular, cleverly conceal their malicious functionality in a separate file named postinstall.js that’s invoked after installation.
That’s because the genuine noblox.js package also employs a file with the same name to display a thank you message to its users alongside links to its documentation and GitHub repository.
The bogus variants, on the other hand, utilize the JavaScript file to verify to see if the package is installed on a Windows machine, and if so, download and execute a second-stage payload hosted on Discord CDN, or alternatively, show an error message.
This is not the first time Luna Token Grabber has been spotted in the wild. Earlier this June, Trellix disclosed details of a new Go-based information stealer called Skuld that overlaps with the malware strain.
“It highlights yet again the trend of malicious actors using typosquatting as a technique to fool developers into downloading malicious code under the guise of similarly named, legitimate packages,” Valentić said.
Source: https://thehackernews.com/