The threat actor behind the information-stealing malware known as Typhon Reborn has resurfaced with an updated version (V2) that packs in improved capabilities to evade detection and resist analysis.
“The stealer can harvest and exfiltrate sensitive information and uses the Telegram API to send stolen data to attackers,” Cisco Talos researcher Edmund Brumaghin said in a Tuesday report.
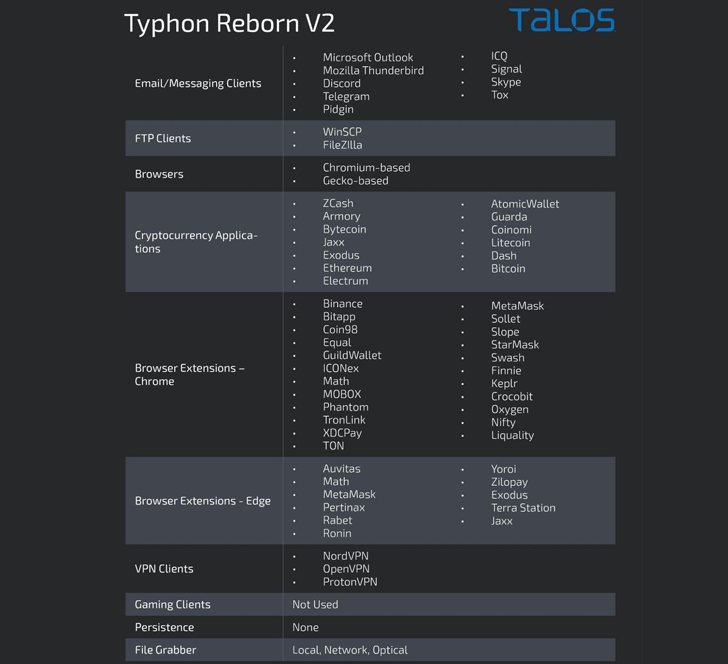
Typhon was first documented by Cyble in August 2022, detailing its myriad features, including hijacking clipboard content, capturing screenshots, logging keystrokes, and stealing data from crypto wallet, messaging, FTP, VPN, browser, and gaming apps.
The latest V2 variant, per Cisco Talos, was marketed by its developer on January 31, 2023, on the Russian language dark web forum XSS.
“Typhon Reborn stealer is a heavily refactored and improved version of the older and unstable Typhon Stealer,” the malware author said, in addition to touting its inexpensive price and the absence of any backdoors.

The malware ultimately transmits the collected data in a compressed archive via HTTPS using the Telegram API, marking continued abuse of the messaging platform.
“Once the data has been successfully transmitted to the attacker, the archive is then deleted from the infected system,” Brumaghin said. “The malware then calls [a self-delete function] to terminate execution.”
The malware is no different from Typhon Reborn in that it’s equipped to siphon cookies and passwords from Chromium-based web browsers as well as data from instant messaging, gaming, and crypto wallet apps.
Source: https://thehackernews.com/