Senior executives working in U.S.-based organizations are being targeted by a new phishing campaign that leverages a popular adversary-in-the-middle (AiTM) phishing toolkit named EvilProxy to conduct credential harvesting and account takeover attacks.
Menlo Security said the activity started in July 2023, primarily singling out banking and financial services, insurance, property management and real estate, and manufacturing sectors.
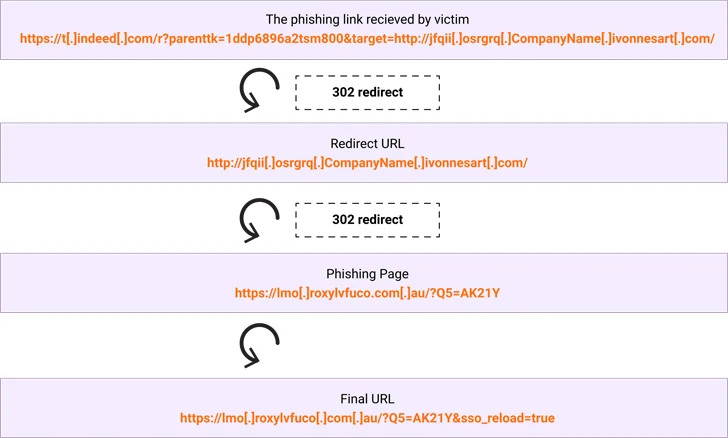
EvilProxy, first documented by Resecurity in September 2022, functions as a reverse proxy that’s set up between the target and a legitimate login page to intercept credentials, two-factor authentication (2FA) codes, and session cookies to hijack accounts of interest.
This is accomplished by taking advantage of an open redirect flaw, which occurs when a failure to validate user input causes a vulnerable website to redirect users to arbitrary web pages, bypassing security guardrails.

“It’s yet another example of how hackers are utilizing legitimate services in what we call BEC 3.0 attacks,” Check Point said. “These attacks are incredibly difficult to stop and identify, for both security services and end users.”
Microsoft, in its Digital Defense Report, noted how “threat actors are adapting their social engineering techniques and use of technology to carry out more sophisticated and costly BEC attacks” by abusing cloud-based infrastructure and exploiting trusted business relationships.
It also comes as the Police Service of Northern Ireland warned of an uptick in qishing emails, which involve sending an email with a PDF document or a PNG image file containing a QR code in an attempt to sidestep detection and trick victims into visiting malicious sites and credential harvesting pages.
Source: https://thehackernews.com/