Exposed Kubernetes (K8s) clusters are being exploited by malicious actors to deploy cryptocurrency miners and other backdoors.
Cloud security firm Aqua, in a report shared with The Hacker News, said a majority of the clusters belonged to small to medium-sized organizations, with a smaller subset tied to bigger companies, spanning financial, aerospace, automotive, industrial, and security sectors.
In total, Kubernetes clusters belonging to more than 350 organizations, open-source projects, and individuals were discovered, 60% of which were the target of an active crypto-mining campaign.
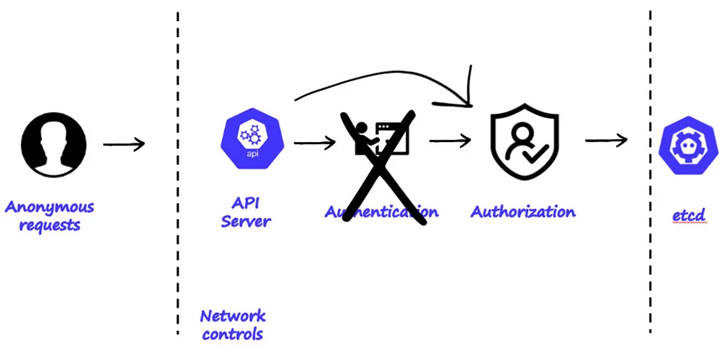
The publicly-accessible clusters, per Aqua, are said to suffer from two different kinds of misconfigurations: allowing anonymous access with high privileges and running kubectl proxy with the flags “–address=`0.0.0.0` –accept-hosts `.*`”

Found among the exposed K8s clusters are pods lists containing sensitive environment variables and access keys that could be exploited by bad actors to burrow deep into the target environment, access source code repositories, and worse, introduce malicious modifications if possible.
A closer examination of the clusters has revealed three different ongoing campaigns aimed at mining cryptocurrency, including a Dero cryptojacking operation, RBAC Buster, and TeamTNT’s Silentbob.
Source: https://thehackernews.com/