A pro-Hamas threat actor known as Gaza Cyber Gang is targeting Palestinian entities using an updated version of a backdoor dubbed Pierogi.
“Recent Gaza Cybergang activities show consistent targeting of Palestinian entities, with no observed significant changes in dynamics since the start of the Israel-Hamas war,” security researcher Aleksandar Milenkoski said in a report shared with The Hacker News.
Gaza Cyber Gang, believed to be active since at least 2012, has a history of striking targets throughout the Middle East, particularly Israel and Palestine, often leveraging spear-phishing as a method of initial access.
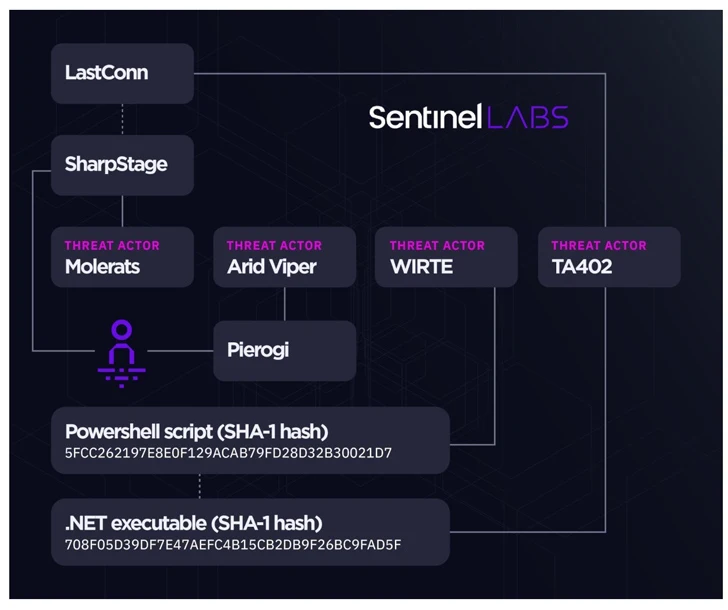
Some of the notable malware families in its arsenal include BarbWire, DropBook, LastConn, Molerat Loader, Micropsia, NimbleMamba, SharpStage, Spark, Pierogi, PoisonIvy, and XtremeRAT among others.
In recent months, the adversarial collective has been linked to a series of attacks that deliver improvised variants of its Micropsia and Arid Gopher implants as well as a new initial access downloader dubbed IronWind.

Cybereason, which shed light on Pierogi in February 2020, described it as an implant that allows attackers to spy on targeted victims and that the “commands used to communicate with the [command-and-control] servers and other strings in the binary are written in Ukrainian.”
SentinelOne’s investigation into Gaza Cyber Gang’s operations have also yielded tactical connections between two disparate campaigns referred to as Big Bang and Operation Bearded Barbie, in addition to reinforcing ties between the threat actor and WIRTE, as previously disclosed by Kaspersky in November 2021.
The sustained focus on Palestine notwithstanding, the discovery of Pierogi++ underscores that the group continues to refine and retool its malware to ensure successful compromise of targets and to maintain persistent access to their networks.
Source: https://thehackernews.com/