Vulnerable Redis services have been targeted by a “new, improved, dangerous” variant of a malware called SkidMap that’s engineered to target a wide range of Linux distributions.
“The malicious nature of this malware is to adapt to the system on which it is executed,” Trustwave security researcher Radoslaw Zdonczyk said in an analysis published last week.
SkidMap was first disclosed by Trend Micro in September 2019 as a cryptocurrency mining botnet with capabilities to load malicious kernel modules that can obfuscate its activities as well as monitor the miner process.
The operators of the malware have also been found camouflaging their backup command-and-control (C2) IP address on the Bitcoin blockchain, evocative of another botnet malware known as Glupteba.
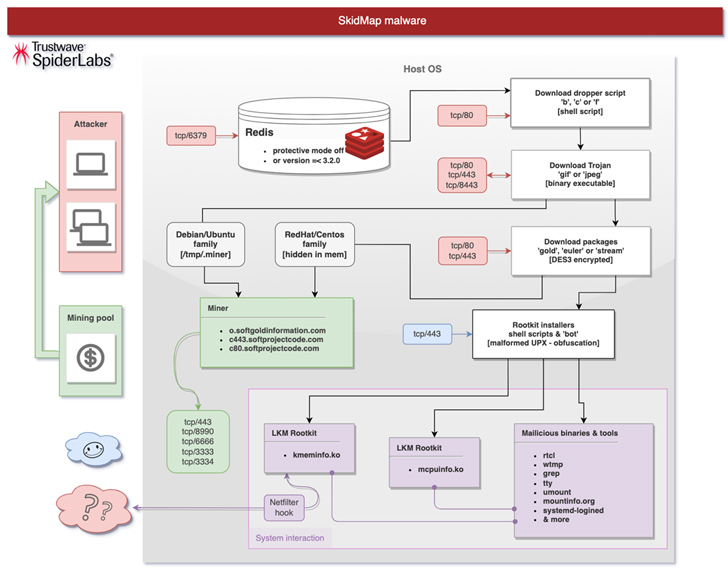
The latest attack chain documented by Trustwave involves breaching poorly secured Redis server instances to deploy a dropper shell script that’s designed to distribute an ELF binary that masquerades as a GIF image file.

The binary then proceeds to add SSH keys to the “/root/.ssh/authoried_keys” file, disable SELinux, establish a reverse shell that pings an actor-controlled server every 60 minutes, and ultimately download an appropriate package (named gold, stream, or euler) based on the Linux distribution and the kernel used.
The package, for its part, comes with several shell scripts to install the kernel modules and take steps to cover up the tracks by purging logs, and launch a botnet component capable of retrieving additional rootkit payloads: mcpuinfo.ko, to hide the miner process, and kmeminfo.ko, to analyze, modify, or drop network packets.
Also downloaded is the miner binary itself, although in some variants, a “built-in miner from an extracted ‘GIF’ binary file” is used.
Source: https://thehackernews.com/